SELinux is a software product that includes several mechanisms that protect against attacks exploiting software vulnerabilities, including attacks on 0-day vulnerabilities. In particular, SELinux implements role-based access control and sandboxing.
SELinux also provides a logging and audit facility that records attempts to exceed specified permissions. By monitoring the system log, the administrator of an SELinux system can often discover attempts to escalate privileges and take action to prevent an intruder or insider from interfering with operation of the system.
SELinux is designed to protect against misuse and unauthorized use such as:
Unauthorized reading of data and programs
Unauthorized modification of data and programs
Bypassing application security mechanisms
Interfering with other processes
Privilege escalation
Information security breaches
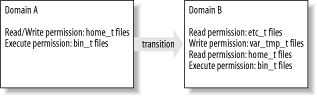
Figure 1-1 depicts the operation of SELinux in a highly simplified fashion. SELinux works by associating each program or process with a sandbox known as a domain. Each domain is assigned a set of permissions sufficient to enable it to function properly but do nothing else. For instance, a domain is limited in the files it can access and the types of operations it can perform on those files. To enable specification of such permissions, each file is labeled with information called a security context. The definition of a domain spells out what operations it can perform on files having specific security contexts. A domain cannot access files having security contexts other than those for which it is explicitly granted access.
Under specified conditions, a process that executes a program leaves its current domain and transitions to a new domain. Typically, transitions occur upon executing a program designated as an entry point to the new domain. The new domain may have more or fewer privileges than the original domain. Thus, programs can initiate other programs having more or fewer privileges than themselves.
An SELinux facility known as type enforcement (TE) ensures that the rules governing domains are always observed. SELinux also has a secondary facility known as role-based access control (RBAC). RBAC limits user access to domains. For instance, some domains are defined to be accessible only to the system administrator, whereas other domains are defined to be publicly available to any user.
An exciting aspect of SELinux is that the definitions of domains, security contexts, and transitions appear in files called policy files that can be modified by the SELinux system administrator. Thus, SELinux security policies are extremely flexible and can support a wide range of security needs. For instance, suppose that you want to install a program that neither you nor anyone you know has previously run under SELinux. Therefore, no policy specifying the operations that the program should and should not be allowed to perform exists. Nevertheless, you can create such a policy and enjoy the benefits of running the program in a manner consistent with the principle of least privilege.
SELinux was originally implemented as a set of Linux kernel modules that worked with the Linux 2.2 kernel. SELinux has since been updated to work with Linux 2.4. SELinux can also work with the Linux Security Modules (LSM) feature of the Linux 2.6 kernel.
LSM consists of a set of hooks inserted into the Linux kernel. These hooks provide the means to notify a software unit, such as SELinux, whenever a process attempts to perform an operation on an object, such as opening a file for read access or deleting a file. LSM also provides a means whereby the software unit can prohibit the attempted access, making it straightforward for software developers to implement a security engine that oversees access to files and other objects, such as that used in SELinux.
In addition to kernel modules, SELinux includes a set of system administration programs that have been modified to be aware of the SELinux environment, and a set of programs used to administer SELinux itself. SELinux also includes a policy, implemented as a set of files, that defines users and roles and their permissions.
Get SELinux now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.