Writing Basic Security Policies
If the SRX could only assign interfaces to zones and allow certain services in and out, there wouldn't be much to it. But the SRX is much more powerful.
After you have zones and interfaces set up, you can tap into the real power of the SRX: the security policies themselves.
Without security policies, all the SRX could do is create interface zones and screen out certain services. Security policies allow you to configure the details of what is and is not allowed through the SRX.
Multiple security policies
Large SRXs can have hundreds or even thousands of policies, because policies become more and more complex as they try and do too much. So, you can have multiple policies that are applied to traffic, all based on source and destination zone. The policies are applied one after another until an action is determined. The final default, of course, is to deny the traffic and discard the packet.
The exception to the default deny rule is traffic on the fxp0 management interface, which makes management of the SRX possible at all times (even when configurations go haywire), and allowing this traffic is a small risk because outside user traffic never appears on this interface.
Figure 12-3 shows this policy ordering on the SRX by zones.
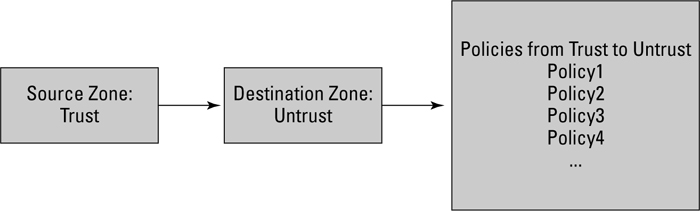
Figure 12-3: SRX zones and policies.
All SRX security policies follow an IF-THEN-ELSE algorithm. IF traffic X matches some rule, ...
Get Junos® OS For Dummies®, 2nd Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

