It’s no accident that this chapter has the word “application” in its title, because the Java security model is solely at the discretion of a Java application. When an applet runs inside the HotJava browser, HotJavaTM is the Java application that has determined the security policy for that applet. And although other popular browsers are not written in Java, they play the role of a Java application: it is still the case that the choice of security model is up to the browser and cannot be changed by the applet.
This makes the distinction between applications and applets a crucial one: applications can establish and modify their security policies while applets (generally) cannot. However, this distinction has diminished over time. Beginning with Java 1.2, users of Java applications have the opportunity to run an application within a sandbox that the user or system administrator has constructed. In the next section, we’ll see how the same functionality can be achieved with Java 1.1 as well. Under these scenarios, the Java security model for applications is solely at the discretion of the user or system administrator.
This is a major change of perception for many users and developers of
Java, who are used to considering the security differences between
applets and applications as a significant differentiator between the
two types of programs. There will, of course, always be particular
programming differences between applets and applications: an applet
extends the java.applet.Applet class and is
written as a series of callbacks, while an application can be any
class that has a static method called main().
When this programming distinction is important, we’ll use the
terms “applet” and “application” as
appropriate. But we’ll typically use the term
“program” to refer to the Java code that we’re
running.
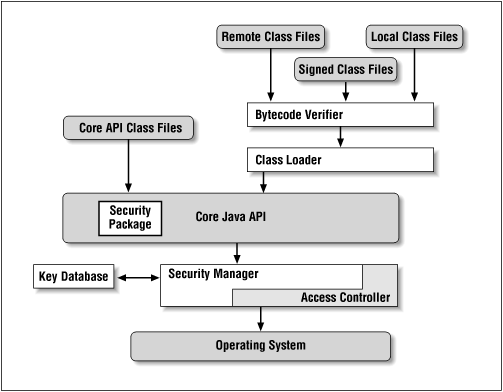
The anatomy of a typical Java application is shown in Figure 1.2. Each of the features of the Java platform that appears in a rectangle plays a role in the development of the Java sandbox. In particular, the elements of the Java sandbox are comprised of:
- The bytecode verifier
The bytecode verifier ensures that Java class files follow the rules of the Java language. In terms of resources, the bytecode verifier helps enforce memory protections for all Java programs. As the figure implies, not all files are subject to bytecode verification.
- The class loader
One or more class loaders load classes that are not found on the
CLASSPATH. In 1.2, class loaders are responsible for loading classes that are found on theCLASSPATHas well.- The access controller
In Java 1.2, the access controller allows (or prevents) most access from the core API to the operating system.
- The security manager
The security manager is the primary interface between the core API and the operating system; it has the ultimate responsibility for allowing or preventing access to all system resources. In 1.2, the security manager uses the access controller for most (but not all) of those decisions; in 1.0 and 1.1, the security manager is solely responsible for those decisions.
- The security package
The security package (that is, classes in the
java.securitypackage) forms the basis for authenticating signed Java classes. Although it is only a small box in this diagram, the security package is a complex API, and discussion of it is broken into several chapters of this book. This includes discussions of:The security provider interface—the means by which different security implementations may be plugged into the security package
Message digests
Keys and certificates
Digital signatures
Encryption (an optional extension to the security package)
The security package was initially available in Java 1.1.
- The key database
The key database is a set of keys used by the security manager and access controller to verify the digital signature that accompanies a signed class file. In the Java architecture, it is part of the security package, though it may be manifested as an external file or database.
The last two items in this list have broad applicability beyond expanding the Java sandbox. With respect to the sandbox, digital signatures play an important role, because they provide authentication of who actually provided the Java class. As we’ll see, this provides the ability for end users and system administrators to grant very specific privileges to individual classes or signers. But a digital signature might be used for other applications. Let’s say that you’re deploying a payroll application throughout a large corporation. When an employee sends a request to view his payroll information, you really want to make sure that the request came from that employee rather than from someone else in the corporation. Often, this type of application is secured by a simple password, but a more secure system could require a digitially signed request before it sent out the payroll information.
We’ll discuss security concerns in both these contexts in this book. In particular, two different examples will form the theme of the examples that are developed through this book:
A browser-type program (called
JavaRunner) that we’ll use to explore the sandbox aspects of Java’s security modelThe payroll application of a large company (XYZ Corporation) that we’ll use to explore how the features of Java’s security model can be used for purposes other than the sandbox (e.g., to sign a payroll request)
We’ll develop a full implementation of the first of these examples; while we won’t provide a complete payroll application, we will provide a number of examples of the security features required for such an application.
Get Java Security now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.