Opening the Black Box
Trying to infer the function of a server side script by modifying its inputs will only get you so far. To really understand its function, you need to open up the Black Box by looking at its source code.
In most instances, this is extremely difficult to do. Unless the site operator has made a serious error in configuring the web server, trying to access a script from a web browser will execute the script, rather than listing it. If that were not the case, then anyone could view and copy any script on the Web. There appears to be no way to do itâwith one exception!
Hitting the Jackpot
In order for this approach to work, you must first lead a virtuous life, be kind to animals, and always give up your seat on the bus to the elderly. Only then, if you are very lucky, might you find a directory listing on a web site such as the one in Figure 5-6.
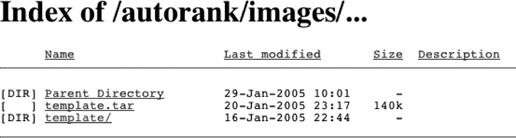
Figure 5-6. Directory listing showing a tar file
This is taken from a phishing site that has been inserted into a legitimate web site. Somehow an attacker has gained access to the system and has inserted all the files necessary to operate a fake bank web site. To make this process convenient, all the necessary files have been packaged into a single tar file and transferred to the hijacked server. The file was then unpacked to create the template directory shown in the figure, as well as several subdirectories.
But this attacker ...
Get Internet Forensics now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

