Internet Forwarders
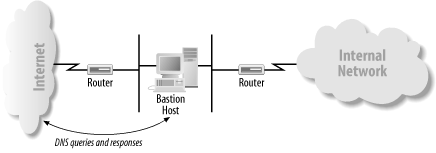
Given the dangers of allowing bidirectional DNS traffic through the firewall unrestricted, most organizations elect to limit the internal hosts that can “talk DNS” to the Internet. With an application gateway firewall, or any firewall without the ability to pass DNS traffic, the only host that can communicate with Internet name servers is the bastion host (see Figure 16-3).
 |
With a packet-filtering firewall, the firewall’s administrator can configure the firewall to let any set of internal name servers communicate with Internet name servers. Often, a small set of hosts runs name servers under the direct control of the network administrator (see Figure 16-4).
 |
Internal name servers that can query name servers on the Internet directly don’t require any special configuration. Their root hints files contain the Internet’s root name servers, which enables them to resolve Internet domain names. Internal name servers that can’t query name servers on the Internet, however, need to know to forward queries they can’t resolve to one of the name servers that can. This is done with the Forwarders tab on the server’s Properties window, described in Chapter 11
Get DNS on Windows Server 2003, 3rd Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

