Firewall Access Rules
As mentioned before, the appropriate method for implementing firewall rules is based on a policy. The policy (on paper) drives what the firewall configuration should be. You can implement many different types of access rules on a typical firewall, some of which are described in Table 14-10.
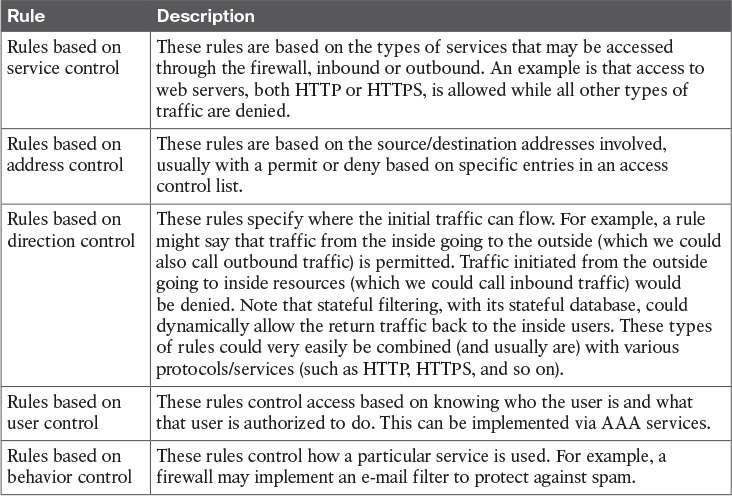
Table 14-10 Firewall Access Rules
Get Santos:CCNA Sec 210-260 OCG now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

