CHAPTER 5
Managing Security
IN THIS CHAPTER
Using NTFS, file share, and registry permissions
Working with the Windows Firewall
Configuring Remote Desktop
You can manage permissions on file, folder, and registry objects with the Get-Acl and Set-Acl cmdlets. As the names imply, these cmdlets retrieve or modify the access control list (ACL) for a file, folder, or registry key. The object returned by the Get-Acl cmdlet is actually a security descriptor, which includes the access control list. The Get-Acl cmdlet, when run on its own, returns nearly useless data unless piped through to either the Format-List cmdlet or one of the export cmdlets like Export-Csv. All of the examples in this chapter that require you to view the ACL use Format-List, whereas all of the examples that save the ACL to a file use the Export-Csv cmdlet. If you are going to modify the ACL, and then reapply it with the Set-Acl cmdlet, you will not necessarily output the result of the Get-Acl cmdlet to screen.
The first part of this chapter builds on the section “Setting Security on Files and Folders” introduced in Chapter 3, “Managing Windows 7.”
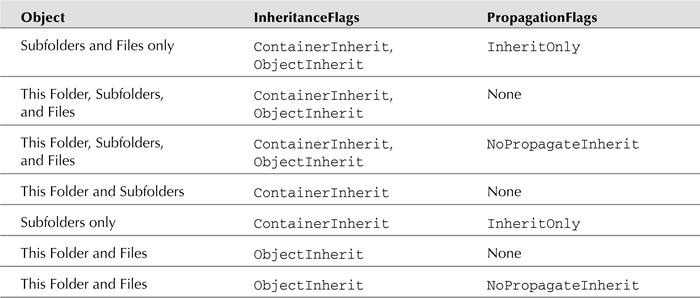
Table 5-1 lists some of the inheritance and propagation flags that can be set on various objects. The Set-Acl cmdlet writes the security descriptor to an object.
TABLE 5-1 Common Inheritance and Propagation Flags for Use with the Set-Acl Cmdlet
Note
For more on propagation ...
Get Windows PowerShell® 2.0 Bible now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

