Up to now, we’ve focused on configuring and using Samba as the primary domain controller. If you already have a domain controller on your network, either a Windows NT/2000 Server system or a Samba PDC, you can add a Samba server to the domain as a domain member server. This involves setting up the Samba server to have a computer account with the primary domain controller, in a similar way that Windows NT/2000/XP clients can have computer accounts on a Samba PDC. When a client accesses shares on the Samba domain member server, Samba will pass off the authentication to the domain controller rather than performing the task on the local system. If the PDC is a Windows server, any number of Windows BDCs might exist that can handle the authentication instead of the PDC.
The first step is to add the Samba server to the domain by creating a computer account for it on the primary domain controller. You can do this using the smbpasswd command, as follows:
# smbpasswd -j DOMAIN -r PDCNAME -Uadmin_acct%password In this command, DOMAIN is replaced by the
name of the domain the Samba host is joining,
PDCNAME is replaced by the computer name
of the primary domain controller,
admin_acct is replaced by the username of
an administrative account on the domain controller (either
Administrator—or another user in the Administrators
group—on Windows NT/2000, and root on Samba), and
password is replaced with the password of
that user. To give a more concrete example, on our domain that has a
Windows NT 4 Server primary domain controller or a Windows 2000
Active Directory domain controller named SINAGUA,
the command would be:
# smbpasswd -j METRAN -r SINAGUA -UAdministrator%hup8terand if the PDC is a Samba system, we would use the command:
# smbpasswd -j METRAN -r toltec -Uroot%jwun83jbwhere jwun83jb is the password for the root user
that is contained in the smbpasswd file, as we
explained earlier in this chapter.
If you did it right, smbpasswd will respond with
a message saying the domain has been joined. The security
identifier[25] returned to Samba from the PDC is kept in
the file /usr/local/samba/private/secrets.tdb.
The information in
secrets.tdb
is security-sensitive, so make sure to
protect secrets.tdb in the same way you would
treat Samba’s password file.
The next step is to modify the
smb.conf
file. Assuming you are starting with a
valid smb.conf file that correctly configures
Samba to function in a workgroup, such as the one we used in Chapter 2, it is simply a matter of adding the following
three lines to the [global] section:
workgroup = METRAN security = domain password server = *
The first line establishes the name of the domain (even though it
says “workgroup”). Instead of
METRAN, use the name of the domain you are joining. Setting security
to “domain” causes Samba to hand
off authentication to a domain controller, and the
password
server
=
* line tells Samba to find
the domain controller for authentication (which could be the primary
domain controller or a backup domain controller) by querying the WINS
server or using broadcast packets if a WINS server is not available.
At this point, it would be prudent to run
testparm to check that your
smb.conf is free of errors. Then restart the
Samba daemons.
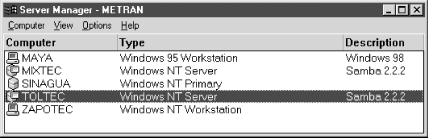
If the PDC is a Windows NT system, you can use Server Manager to check that the Samba server has been added successfully. Open the Start menu, then select Programs, then Administrative Tools (Common), and then Server Manager. Server Manager starts up with a window that looks like Figure 4-16.
As you can see, we’ve added both
toltec and mixtec to a domain
for which the Windows NT 4.0 Server system,
sinagua, is the primary domain controller.
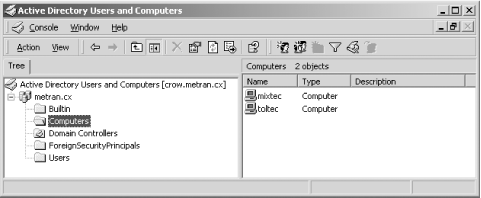
You can check your setup on Windows 2000 Advanced Server by opening the Start menu and selecting Programs, then Administrative Tools, then Active Directory Users and Computers. The window that opens up will look like Figure 4-17.
Click Computers in the left side of the window with the Tree tab. You should see your Samba system listed in the right pane of the window.
[25] This security identifier (SID) is part of an access token that allows the PDC to identify and authenticate the client.
Get Using Samba, Second Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.