Chapter 13. Hashing Algorithms
In the previous chapter, we showed you that Alice and Bob could ensure the integrity of their messages by using data hash codes. Alice creates a hash code, which she sends to Bob along with her message. When Bob receives the message, he creates his own hash code and compares it to the one that he received from Alice. If the two hash codes are the same, then Bob can assume that Eve has not altered the contents of the message.
In this chapter, we examine hash codes in-depth and show you how to create and validate your own hash codes using the .NET Framework classes. We also show you how you can extend the .NET Framework by adding a new hashing algorithm.
Hashing Algorithms Explained
A hashing algorithm creates a hash code, also called a “message digest” or “message fingerprint.” As we explained in Chapter 12, hash codes are of limited use for communications security, because Eve can replace both the hash code and the message that Bob receives, but they are an essential element of digital signatures, which we discuss in Chapter 16.
In this section, we explain how hashing algorithms work, and provide some practical insight into choosing a suitable algorithm for your project.
Creating a Hash Code
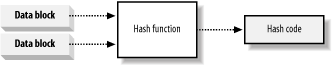
A t the heart of a hashing algorithm is a mathematical function that operates on two fixed-size blocks of data to create a hash code, as shown in Figure 13-1.
 |
Get Programming .NET Security now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

