Overall Flow of Events for Securing the Deployment
The sections of this chapter go through some of key steps for securing the pricing application’s environment. Although these steps are discussed in a particular sequence, they can be carried out separately because they are mostly independent considerations, unless mentioned otherwise. Table 9-1 provides a summary of these steps.
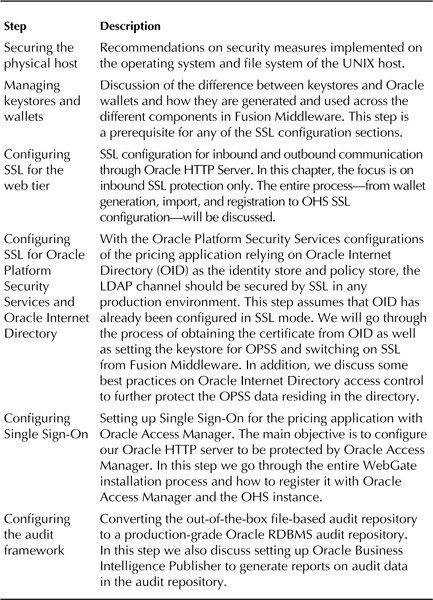
TABLE 9-1. Pricing Application Security Configuration Steps
Get Oracle Fusion Middleware 11g Architecture and Management now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

