Composite Attacks
Composite attacks covers a scenario where the red team is working for a financial services firm and modeling a sophisticated criminal organization, very targeted towards customer financial data.
Keywords
SQL injection; XSS; VPN endpoint
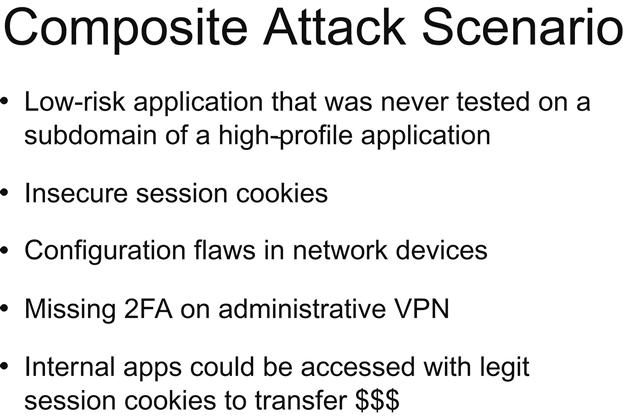
In another composite attack involving a financial services company, we modelled a sophisticated criminal organization that was focused on accessing customer financial data. We found their flagship application had a lot of different security controls in place; everything was very well guarded. On a subdomain of that high-risk flagship application, we found a marketing site, let’s call it marketing ...
Get Next Generation Red Teaming now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

