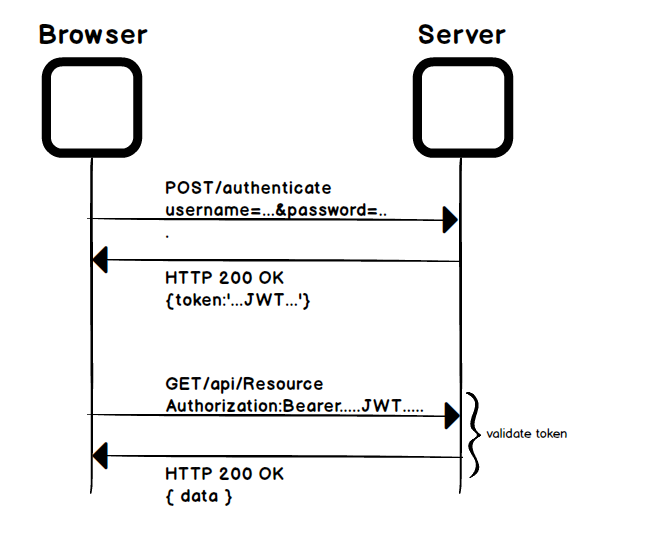
The fundamental concept behind a token-based authentication system is simple. It allows users to enter their username and password in order to obtain a token, and then use this token in every request to fetch a specific resource—without using their username and password again. Once the token has been obtained, the user can offer the token to access the resource for a time period, while the token is valid. This is depicted in the following diagram:
It is stateless and scalable. The server need not store the token in a session or memory (stateless) and hence it is scalable. It is mobile application-ready, secure, ...

