The application can get compromised if an attacker uploads a malicious PHP file by sending a POST request on the /clients/editclient.php?id=1&action=update URL. The code does not validate the request if it's originating from an authenticated user or not. The problematic code is as follows:
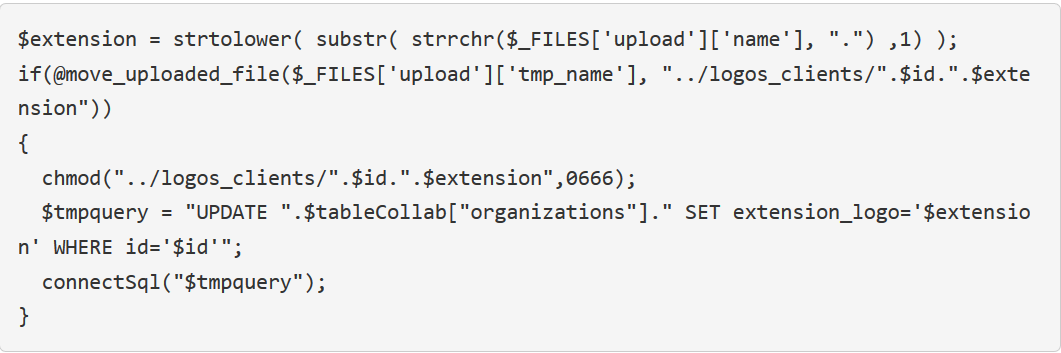
From line number 2, we can see that the uploaded file is saved to the logos_clients directory with the name as $id followed by the $extention, which means that since we have id=1 in the URL, the uploaded backdoor will be saved as 1.php in the logos_clients directory.

