The window_enum feature in the extended API provides us with a list of all the open Windows on the compromised machine. This may allow us to figure out more about the target and the application running on it. Let's see what happens when we run this module on the target system:
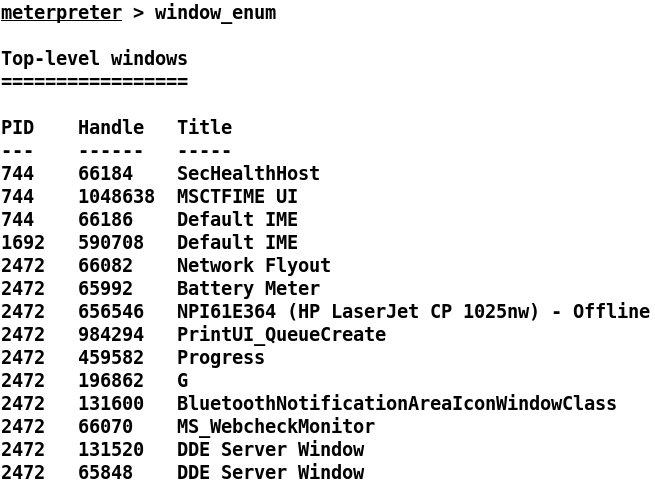
As suggested, we have the list of all the open Windows on the target with their current process IDs. Let's explore some more:
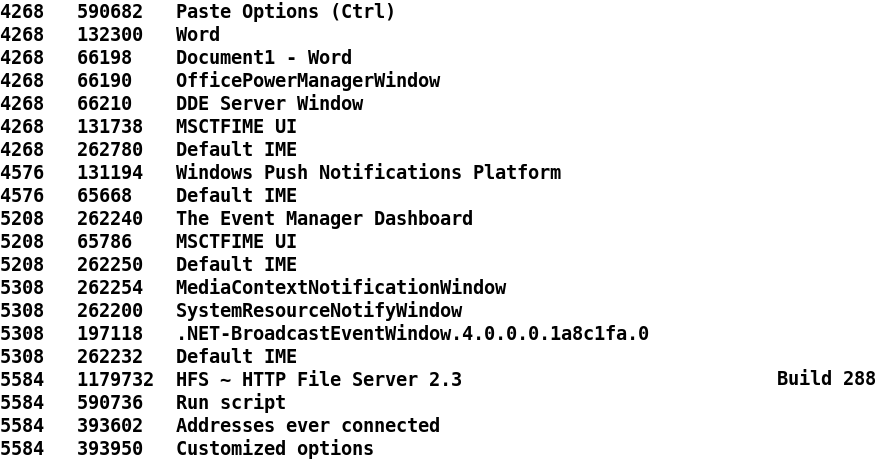
We can see that Microsoft Word is open on the target system, which denotes the presence of a human entity ...

