Shell bind TCP for iOS
At a high level, there could be two types of shell access on the target device. One is a bind shell, where we will run shell on the target device and connect to it. Second is a reverse shell, where we will run shell on the base system to which the target will connect back. You will learn both ways to obtain shell.
Let's follow the given steps to create a bind TCP shell:
- You can check all Metasploit payloads available for
osx/armle. You can use the commandmsfvenom –lto list all payloads: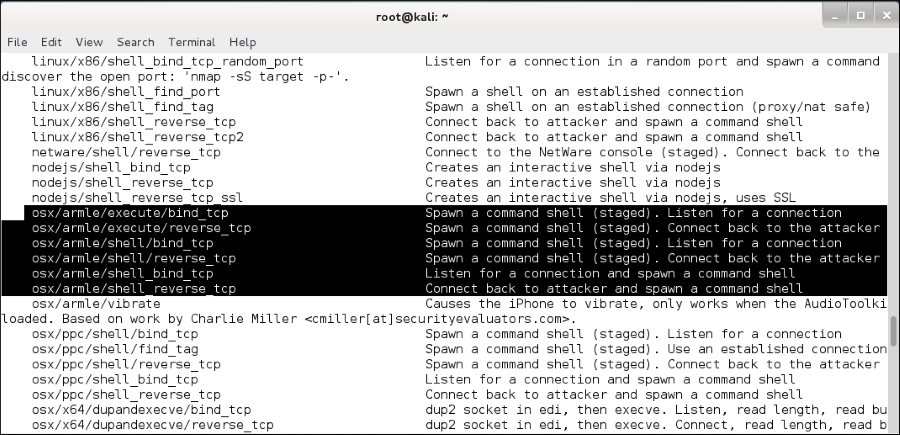
- Select the
shell_bind_tcppayload available forosx/armle: - Now, connect your iDevice using SFTP and transfer the payload file to the
tmpdirectory: ...
Get Learning iOS Penetration Testing now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

