Another thing we do in every red team is to assess the possibility of installing physical devices in the target organization's network.
A typical device could be a Raspberry Pi with features such as mobile broadband, wireless, Ethernet port, and so on:
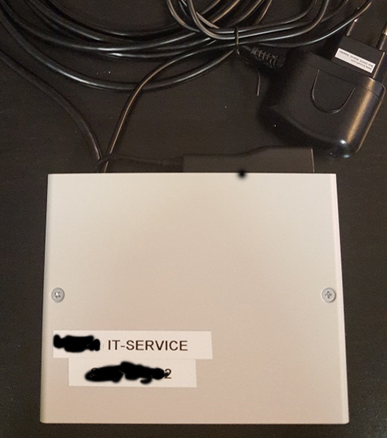
The common security implementation to mitigate the connection unauthorized devices is 802.1X. Because of that, we always install the device between the network port and some already-connected device. Most of the time we prefer to look ...

