Time for action – man-in-the-middle attack
Follow these instructions to get started:
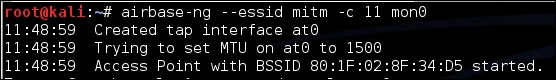
- To create the man-in-the-middle attack setup, we will first create a soft access point called
mitmon the hacker laptop usingairbase-ng. We run the following command:airbase-ng --essid mitm –c 11 mon0The output of the command is as follows:
- It is important to note that
airbase-ng, when run, creates an interfaceat0(a tap interface). Think of this as the wired-side interface of our software-based access pointmitm: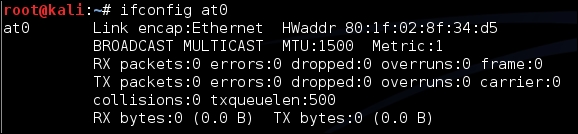
- Let's now create a bridge on the hacker's laptop, ...
Get Kali Linux Wireless Penetration Testing : Beginner's Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

