Time for action – cracking WEP with the Hirte attack
Follow these instructions to get started:
- Create a WEP access point exactly as in the Caffe Latte attack using the
airbase-ngtool. The only additional option is the-Noption instead of the-Loption to launch the Hirte attack: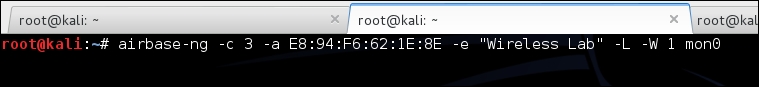
- Start
airodump-ngin a separate window to capture packets for the Wireless Lab Honeypot: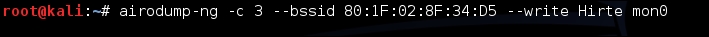
- Now,
airodump-ngwill start monitoring this network and storing the packets in theHirte-01.capfile: - Once the roaming client connects to our Honeypot AP, the Hirte attack is automatically ...
Get Kali Linux Wireless Penetration Testing : Beginner's Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

