Time for action – evil twins and MAC spoofing
Follow these instructions to get started:
- Use
airodump-ngto locate the access point's BSSID and ESSID, which we would like to emulate in the evil twin: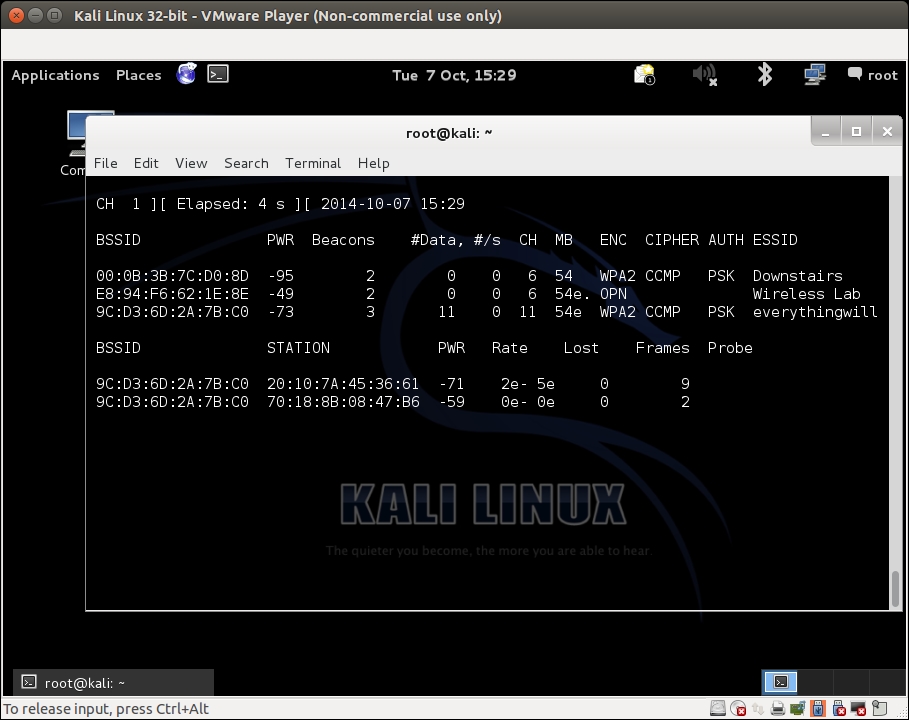
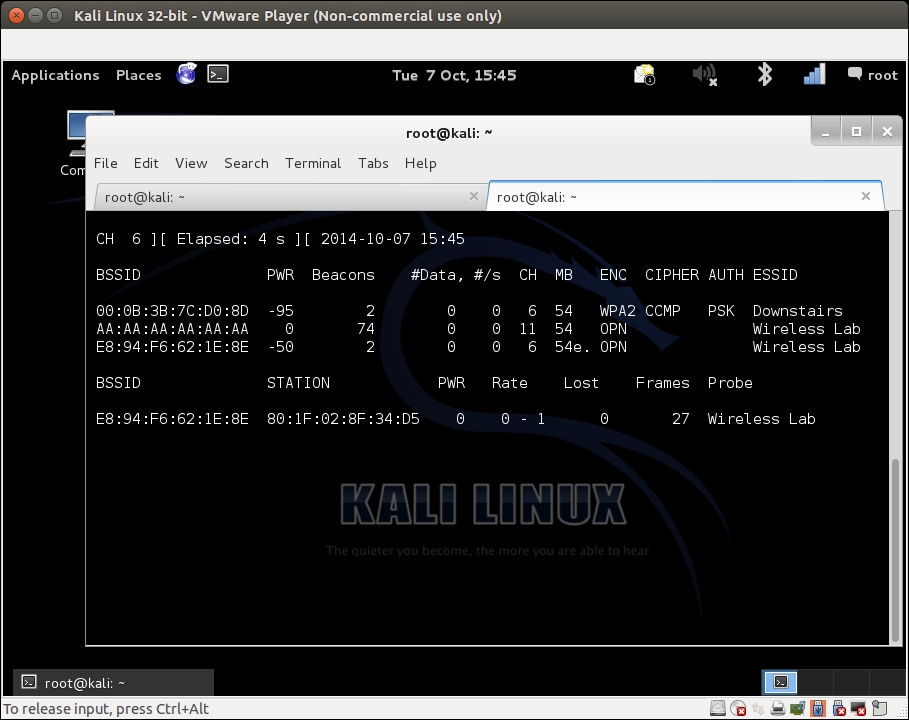
- We connect a Wireless client to this access point:
- Using this information, we create a new access point with the same ESSID but a different BSSID and MAC address using the
airbase-ngcommand. Minor errors may occur with newer releases: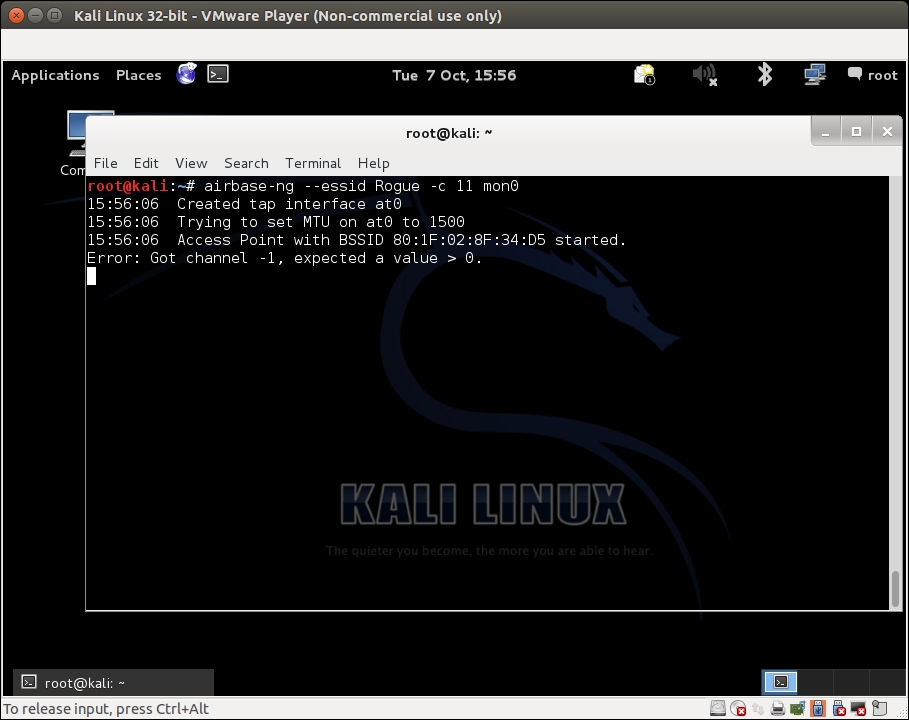
- This new access point ...
Get Kali Linux Wireless Penetration Testing : Beginner's Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

