Time for action – decrypting WEP and WPA packets
We can proceed with the following steps:
- We will decrypt packets from the WEP capture file we created earlier:
WEPCrackingDemo-01.cap. For this, we will use another tool in the Aircrack-ng suite calledairdecap-ng. We will run the following command, as shown in the following screenshot, using the WEP key we cracked previously:airdecap-ng -w abcdefabcdefabcdefabcdef12 WEPCrackingDemo-02.cap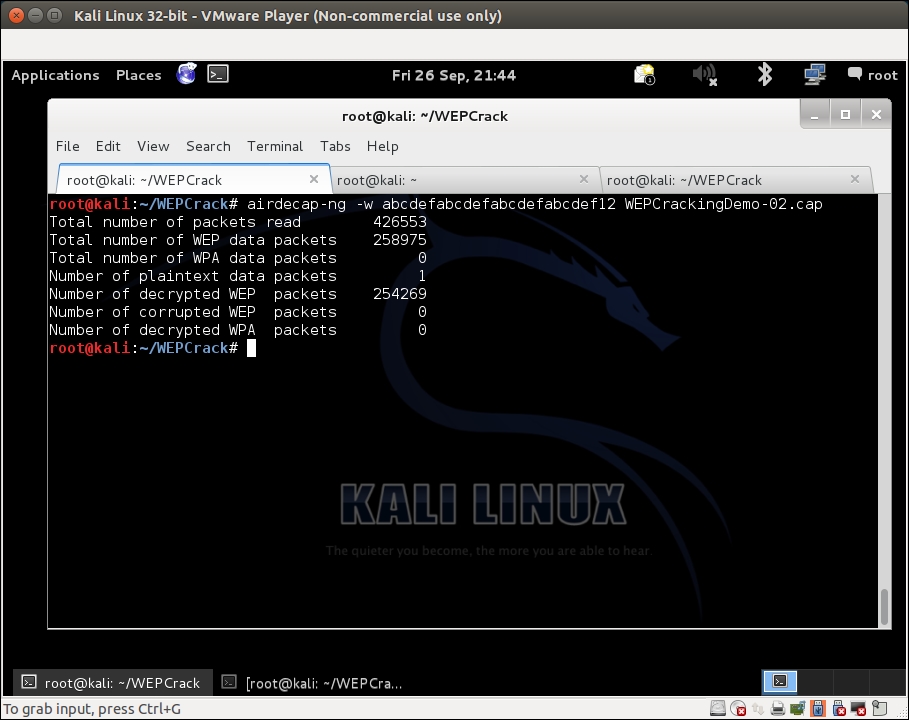
- The decrypted files are stored in a file named
WEPCrackingDemo-02-dec.cap. We use thetsharkutility to view the first ten packets in the file. Please note that you may see something different based on what you ...
Get Kali Linux Wireless Penetration Testing : Beginner's Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

