Multihome Beer-Co
Beer-Co’s initial BGP peering with Botnet in AS 34 is operating successfully, and it’s time to bring up a second EBGP session to Borgnet in AS 420. When multihomed to dual providers, the true benefit of BGP and its policy controls can be fully realized. Figure 7-9 provides the new BGP peering topology and illustrates how Borgnet connects to service provider Darknet in AS 666, which is also peered with Botnet. It seems that things could get quite interesting here.
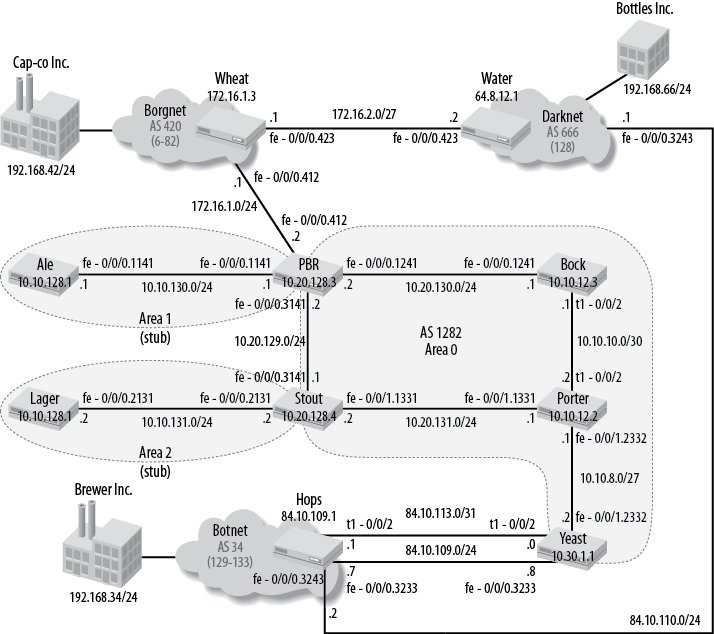
Figure 7-9. Beer-Co goes multihomed with a connection to Borgnet
The figure shows key details of each AS. These include the EBGP peering router’s name, its loopback address, and the set of routes that originate within that AS and the customer routes associated with that network. The figure calls out three particular customer prefixes within Borgnet, Darknet, and Botnet, which are assigned to customers Cap-co Inc., Bottles Inc., and Brewer Inc., respectively. The 192.168.xx/24 prefixes associated with these extranet partners demonstrate the effects of inbound and outbound policy actions in the following sections.
In this scenario, Beer-Co’s IGP consists of an area 0 backbone with
two stub areas. Area border routers (ABRs) PBR and Stout
originate an OSPF default route into their respective stub areas.
The design goals for the new BGP peering arrangement are as follows:
Deploy new import policy at routers
Yeast ...
Get Junos Enterprise Routing, 2nd Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

