Part II
Putting Ethical Hacking in Motion
In this part . . .
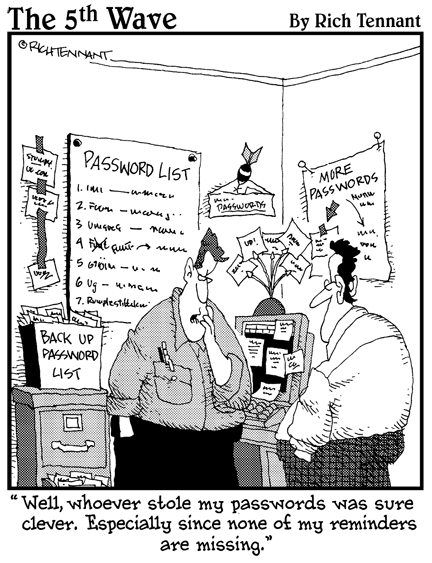
Let the games begin! Youâve waited long enough â nowâs the time to start testing your systems. But where do you start? How about with your three Ps â your people, your physical systems, and your passwords? These are, after all, three of the most easily and commonly attacked targets in your organization.
This part starts with a discussion of hacking people (as opposed to hacking up people; this is social engineering, not The Texas Chainsaw Massacre). It then goes on to look at physical security vulnerabilities. Of course, Iâd be remiss in a part about people if I skipped passwords, so I cover the technical details of testing those as well. This is a great way to get the ball rolling to warm you up for the more specific hacks later in the book.
Get Hacking For Dummies, 4th Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

