2.4 EXAMPLES OF CRIBBING
Example 2.2
The ciphertext is of length n = 446:
____________________________________________________________
cipherEx2.2
____________________________________________________________
m c g trfttsaocehyhrsayohalolcintTm cgt s ilcdlCtf aunods ng
c ea e ts enuuc nnrcog e eam otsliy, ukrsima meuc aUotxgits
nmotr tad inw e wafscfuus ttihdea dri d.yptlo in 2rtsatmts
s tipmCvhc ecepnhors oldlwc iin iids,irornsraaeow acT tcg
cuemar blte nos ornoaBrstua p eosrsiro skdins eerfn ,nad.Cee
ae mp onle ,ueouov wf4 e teuiy.ceer Seiimfdi.l ige bbfl ehau
ndgaoecyi nypseuodii hhtddorn e nsmone locsehpser c enteiio
i pml aykaoehbd roasitbsds
____________________________________________________________
We assume it is known that plainEx2.2 is from a 1982 UCSB Computer Science Department brochure. It is therefore reasonable to assume computer science, Computer science, or Computer Science as possible cribs.
2.4.1 Testing Possible Widths
Table 2.10 lists the subcribs of computer science for widths 5 ≤ N ≤ 9.
Table 2.11 contains the output of the program Search1, which lists all subcribs of computer science that do not occur in y:
| Search1 | |
| Input: | Interval of widths N0 ≤ N ≤ N1, (w, y) |
| Output: | All subcribs of w which do not occur in y |
TABLE 2.10 The Subcribs of computer science for 5 ≤ N ≤ 9
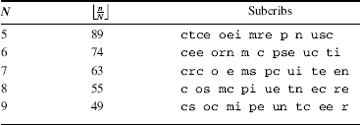
TABLE 2.11 Output of Search1 for computer science width 5 ≤ N ≤ 9
| N | Subcribs ... |
Get Computer Security and Cryptography now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

