CHAPTER 10
NETWORK SECURITY1
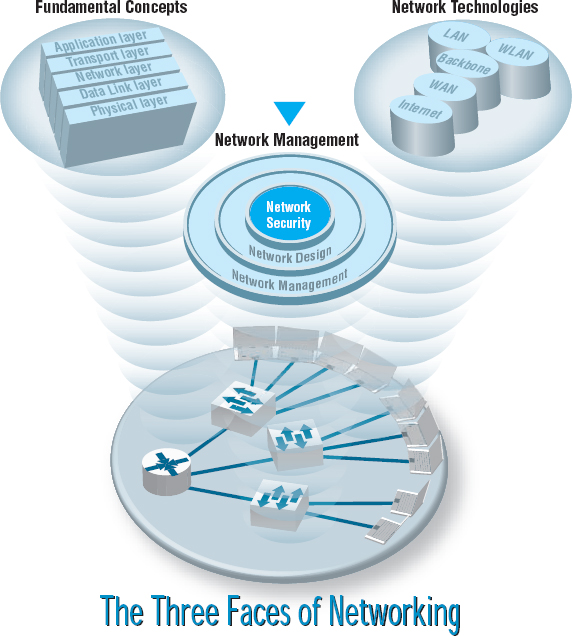
THIS CHAPTER describes why networks need security and how to provide it. The first step in any security plan is risk assessment, understanding the key assets that need protection, and assessing the risks to each. There are a variety of steps that can be taken to prevent, detect, and correct security problems due to disruptions, destruction, disaster, and unauthorized access.
OBJECTIVES ![]()
- Be familiar with the major threats to network security
- Be familiar with how to conduct a risk assessment
- Understand how to ensure business continuity
- Understand how to prevent intrusion
CHAPTER OUTLINE ![]()
10.1.1 Why Networks Need Security
10.1.2 Types of Security Threats
10.2.1 Develop a Control Spreadsheet
10.2.2 Identify and Document the Controls
10.2.3 Evaluate the Network's Security
10.3 ENSURING BUSINESS CONTINUITY
10.3.2 Denial of Service Protection
10.3.4 Device Failure Protection
10.4.2 Perimeter Security and Firewalls
Get Business Data Communications and Networking, Eleventh Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

