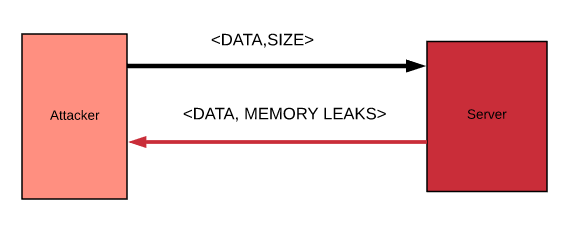
In a Heartbleed attack, the attackers exploit the TLS heartbeat extension in the OpenSSL library. This extension is used to always ensure that the connection between two systems is alive. The request payload is composed of the data and the size of it. The attackers exploit this format to force the server to send the requested size from leaked data from memory:
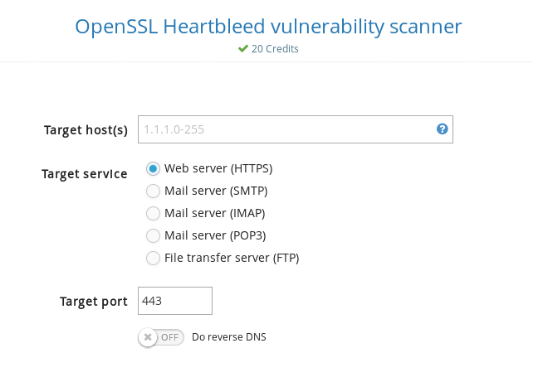
In order to test your servers, try the usual website: